Tamper-Proof RFID Tags for Electronics Security Applications
In today’s interconnected world, electronics are everywhere—from critical infrastructure and medical devices to consumer gadgets and automotive systems. With this proliferation comes an uncomfortable truth: these assets are increasingly vulnerable to tampering, counterfeiting, and unauthorized access. For businesses that manufacture, deploy, or manage electronic assets, security is no longer just an IT concern—it is a physical one.
That is where tamper-proof RFID tags for electronics security applications enter the picture. These specialized tags do more than just identify an asset; they actively protect it. By combining robust physical construction with intelligent detection capabilities, they offer a level of security that traditional tracking methods simply cannot match. And when integrated thoughtfully, RFID tags for electronics become a cornerstone of modern asset protection strategies.
Why Standard Tracking Isn’t Enough for Security
Most people associate RFID with inventory management—scanning pallets, tracking tools, or managing retail stock. And yes, RFID tags for electronics excel at those tasks. But when the stakes involve security, standard tags fall short. A conventional RFID tag can be removed from one device and attached to another without triggering any alert. In environments where authenticity matters—think medical implants, server hardware, or high-value components—this vulnerability is unacceptable.
Tamper-proof tags solve this problem by changing the rules entirely. They are designed to detect interference, report breakage, and make unauthorized removal immediately obvious. For organizations that cannot afford to gamble on the integrity of their electronics, this capability transforms RFID from a convenience into a necessity.
What Makes a Tamper-Proof RFID Tag Different?
The phrase “tamper-proof” covers several distinct technologies, each suited to different electronics security applications. Understanding these differences helps in selecting the right solution.
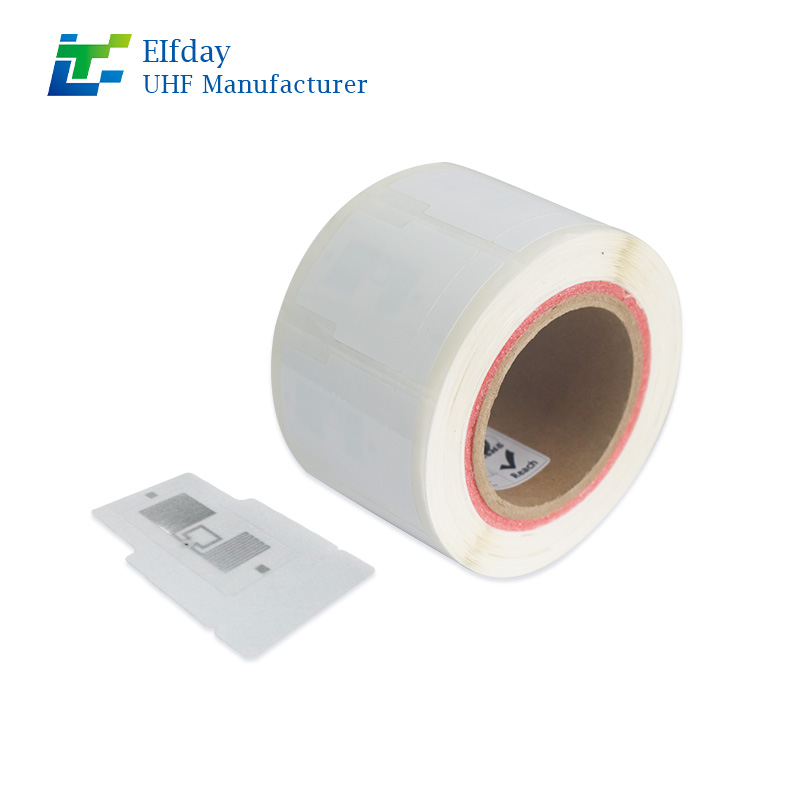
Breakaway or Destructible Designs
Some tamper-proof RFID tags are engineered to physically break the moment someone tries to peel them off. The antenna is embedded in a way that removal tears it apart, making the tag permanently unreadable. This is particularly useful for warranty seals, authentication labels, and high-value consumer electronics. Once the tag is compromised, it cannot be reused or reattached without immediate detection.
Tamper Loops and Conformal Designs
For applications where the tag is wrapped around a cable, connector, or enclosure, tamper-loop designs are common. These tags use a thin conductive loop that, when cut or severed, triggers a change in the tag’s response. They are widely used in data centers to secure server racks, in transportation to seal cargo containers, and in telecommunications to protect infrastructure equipment.
Cryptographic Authentication
Beyond physical breakage, advanced RFID tags for electronics incorporate cryptographic features. Each tag contains a unique, unclonable identifier that communicates with the reader using encrypted protocols. Even if someone manages to physically remove the tag intact, they cannot replicate its digital identity. This makes counterfeiting far more difficult—a critical advantage for brands battling gray market goods or unauthorized component replacements.
Encapsulated and Overmolded Tags
In harsh environments, physical tampering is not the only concern. Moisture, vibration, and temperature extremes can also compromise a tag’s integrity. Tamper-proof tags designed for electronics security often feature rugged encapsulation—epoxy, ceramic, or high-grade polymer housings—that resist environmental attack while maintaining their anti-tamper functionality. These are common in military electronics, industrial control systems, and outdoor infrastructure.
Where Tamper-Proof RFID Tags Make the Biggest Impact
The versatility of tamper-proof RFID tags for electronics means they find their way into a surprisingly wide range of security applications. Each scenario demands a slightly different approach, but the underlying principle remains the same: trust but verify.
Data Center and IT Asset Security
Data centers house thousands of servers, storage arrays, and networking devices. These are not only expensive to replace but also contain sensitive data. Unauthorized removal or replacement of a server can lead to data breaches or service disruptions. By applying tamper-proof RFID tags to each chassis, data center operators gain the ability to scan racks instantly and detect any device that has been moved, swapped, or removed without authorization. Some organizations go a step further, integrating tag reads with access control systems so that any tamper event triggers an immediate alert to security personnel.
Medical Electronics and Implantable Devices
In the medical field, the integrity of electronic devices is a matter of patient safety. Defibrillators, infusion pumps, and surgical tools must be authentic and untampered. Tamper-proof RFID tags applied to these devices provide a chain of custody that regulatory bodies increasingly expect. If a device is opened, refurbished with non-certified parts, or removed from its authorized location, the tag records the event. For hospitals and medical device manufacturers, this traceability supports compliance, reduces liability, and ultimately protects patients.
Supply Chain and Anti-Counterfeiting
Counterfeit electronics are a multibillion-dollar problem. Fake components find their way into everything from automotive braking systems to aerospace avionics. Tamper-proof RFID tags for electronics applied at the point of manufacture create a verifiable chain of authenticity. Distributors and end-users can scan tags to confirm that a component is genuine and has not been intercepted or swapped during transit. For original equipment manufacturers, this capability preserves brand reputation and reduces the risk of field failures caused by counterfeit parts.
Critical Infrastructure and Industrial Control
Power grids, water treatment facilities, and telecommunications networks rely on electronic control systems that must remain secure from physical interference. Tamper-proof RFID tags on control cabinets, remote terminal units, and communication gear enable rapid security audits. If a cabinet door is opened or a module is removed, the tag registers the event, allowing security teams to investigate immediately. In industries where safety and uptime are paramount, this level of visibility is not optional—it is essential.
Consumer Electronics and Warranty Management
For consumer electronics brands, protecting the warranty lifecycle is both a financial and reputational concern. Tamper-proof tags embedded in products like laptops, smart home devices, or gaming consoles help distinguish legitimate warranty claims from those involving unauthorized repairs or modifications. When a device arrives for service, scanning the tag instantly tells the technician whether the original seal is intact. This reduces fraud, streamlines warranty processing, and ensures that customers receive appropriate support.
Beyond Physical Security: The Business Case
Investing in tamper-proof RFID tags for electronics is not just about preventing theft or counterfeiting—it is about building trust across the entire business ecosystem.
Strengthening Customer Confidence
When customers know that a product is authenticated and its integrity has been maintained from factory to field, their confidence grows. This is especially valuable in premium markets where authenticity and quality are key differentiators. A simple scan with a smartphone or handheld reader can reassure end-users that they have received a genuine, unaltered product.
Streamlining Audits and Compliance
Regulatory frameworks in industries like medical devices, aviation, and defense increasingly require documented chain of custody. Manual records are time-consuming and error-prone. Tamper-proof RFID automates this documentation, making audits faster and less burdensome. Compliance officers can generate detailed reports showing exactly when and where a device was scanned, and whether any tamper events occurred.
Reducing Liability and Operational Risk
A counterfeit component that fails in the field can cause catastrophic damage—both financially and reputationally. By implementing tamper-proof RFID tags for electronics in critical supply chains, organizations significantly reduce the risk of using unauthorized parts. This proactive approach to risk management appeals to insurers, regulators, and board-level stakeholders who prioritize operational resilience.
Choosing the Right Tamper-Proof RFID Solution
No single tag works for every electronics security application. The right choice depends on the environment, the asset, and the specific threat model.
For high-value consumer electronics, a destructible adhesive tag with a unique cryptographic ID often provides the right balance of cost and security. These tags are applied during final assembly and are meant to be visible to consumers as a trust indicator.
For industrial or infrastructure assets, rugged encapsulated tags with tamper loops are more appropriate. These can withstand outdoor conditions, vibration, and years of service while continuing to report their status.
For medical or aerospace applications, the focus shifts to materials compatibility and sterilization resistance. Tamper-proof tags used in these settings must withstand autoclaving, chemical cleaning, or extreme temperatures without losing their anti-tamper properties.
Working with an experienced RFID provider makes a significant difference. The right partner helps evaluate the application, select appropriate tag form factors, and ensure seamless integration with existing security systems and workflows.
Implementation Considerations
Adding tamper-proof RFID to a security strategy does not require a complete overhaul of existing systems. Most deployments follow a phased approach:
Start with a pilot program focused on the most critical assets—perhaps a single data center row, a specific product line, or a high-value inventory zone. This allows teams to refine workflows, test reader placements, and validate tag performance before scaling.
Integrate tag reads with existing access control or asset management software. The goal is not to create another isolated system but to enrich the visibility already available to security and operations teams.
Train personnel on what tamper events look like and how to respond. A tamper alert is valuable only if it triggers the right action—whether that is a security investigation, a quality hold, or a simple notification to maintenance staff.
The Future of Electronics Security
As electronics become smaller, more powerful, and more deeply embedded in everyday life, the need for physical security will only intensify. Tamper-proof RFID tags for electronics represent a practical, scalable way to meet that need. They bridge the gap between digital identity and physical integrity, giving organizations confidence that what they track is exactly what they have.
For businesses that manufacture, deploy, or rely on electronic assets, this capability is no longer a luxury. It is a competitive necessity. In a world where a single compromised component can ripple across an entire operation, investing in tamper-proof RFID is an investment in trust, reliability, and long-term resilience.
Ready to Secure Your Electronics?
If you are responsible for protecting electronic assets—whether in a manufacturing environment, a data center, or a global supply chain—tamper-proof RFID tags for electronics deserve a close look. The technology has matured, the costs have become accessible, and the applications are more varied than ever.
Our team specializes in helping organizations identify the right RFID solutions for their unique security challenges. From selecting the appropriate tag type to integrating with existing systems, we provide the expertise needed to move from concept to deployment with confidence.
Contact us today to discuss how tamper-proof RFID can strengthen your electronics security strategy.